March 2015 Issue
Topics
Developing strategies to counter cyber-attacks on industrial infrastructure

Info-Powered Energy System Research Center

Department of Mechanical Engineering and Intelligent Systems
Graduate School of Informatics and Engineering
Cyber-attacks, computer viruses, and hacking are terms synonymous with unapproved access of computer systems managed by banks and national security organizations. However, such 'cyberattacks' have recently been directed at factories and manufacturing plants, power stations, and even water purification facilities.
"The proliferation of factory automation based on computer networks connected to the internet has led to a dramatic increase in malicious cyber-attacks on such facilities," says Professor Seiichi Shin, at Department of Mechanical Engineering and Intelligent Systems, University of Electro-Communications, Tokyo. "A critical change in the pattern of cyberattacks was seen with the Stuxnet computer worm attack on a nuclear power plant in 2010. This incident and the massive damage caused by the Great Tohoku Earthquake on 11 March 2011 led to the Japanese Government to establishment the 'Control System Security Center' (CSSC) in 2012. I am the president of the CSSC and UEC is the base for our activities."
Notably, in contrast to governmental cyber security groups in the USA and EU that are managed by national defense organizations, the majority of the 30 members of the CSSC are industrialists from Japan's top-tier private companies. "The members share information without compromising know-how and intellectual property rights," says Shin. "The key in our strategy is to mix our knowledge of information and control systems. This is crucial because attacks on manufacturing plants use the information networks to disrupt production processes. So the CSSC has experts from both technology sectors. "
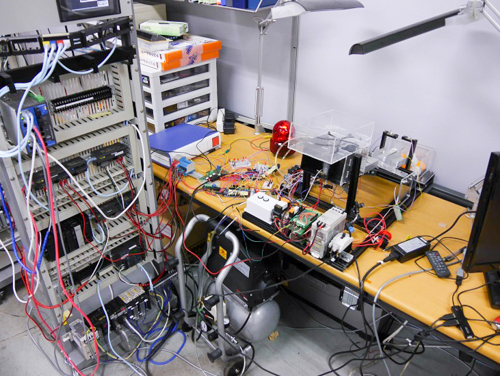
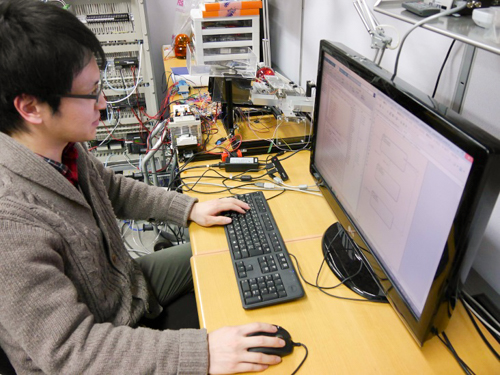
Kenji Sawada, associate professor at the Info-Powered Energy System Research Center, at UEC Tokyo, is a member of the Shin Group, and is responsible for developing models for countering cyberattacks on critical manufacturing facilities of factories. "Our models are based on risk assessment analysis," says Sawada. "Recently I worked with graduate school student Mr Tsubasa Sakaki on the construction of an actual model to simulate a cyberattack on the production line of a factory." The model separates heavy (golf balls) and light (table tennis balls) balls on a conveyer belt and simulates a simple defective discriminator. In the simulation, a virus takes control of actuators and creates havoc with the sorting process. A potentially hazardous situation is detected by comparing the model behavior with the actual behavior and averted by removing control from the remote controller (connected to the internet via Windows software) to a local 'micon' based controller that is not connected to the internet. Such the strategy is named as model-based fallback control.
"Monitoring and preventing cyberattacks in industrial facilities is an important aspect of the increasingly interconnected world," says Shin. "Ordinary households are also vulnerable. So called 'smart meters' for monitoring power consumption and security systems are linked to the internet. Our research at UEC and the Control System Security Center is also aimed at mitigating attacks on such systems for the peace of mind of residents of Japan."
References
Seiichi Shin, A status of Control System Security in Japan, The 10th Asian Control Conference 2015, May 31th - June 3rd, 2015.
Kenji Sawada, Tsubasa Sasaki, Seiichi Shin, Shu Hosokawa, A Fallback Control Study of Networked Control Systems for Cybersecurity, The 10th Asian Control Conference 2015, May 31th - June 3rd, 2015.
Websites: http://www.shinlab.mi.uec.ac.jp/


